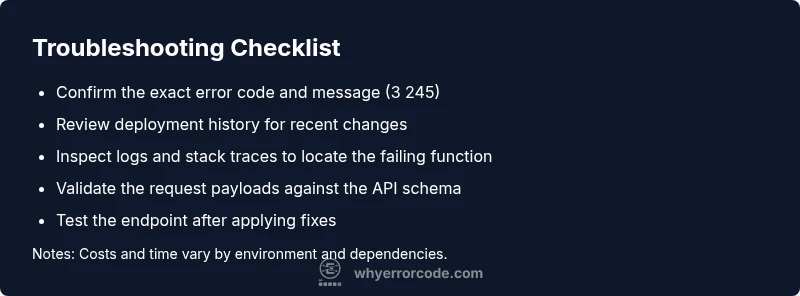
Backend Error Code 3 245 Meaning: Urgent Diagnostics and Fixes
Understand backend error code 3 245 meaning, its symptoms, common causes, and urgent fixes with practical, step-by-step guidance to restore services quickly and safely.
Backend error code 3 245 means a server-side operation failed during a critical step, often indicating a permission or data validation mismatch. The fastest fix is to restart the failed service, check recent deployments, and verify the implicated endpoint's input validation. If symptoms persist, review logs for the exact failing function and apply targeted patches.
What backend error code 3 245 meaning
Backend error code 3 245 is a server-side signal that a critical operation halted during processing. It usually points to a constraint violation, a permissions issue, or a data validation failure rather than a problem with the client request. The precise interpretation can vary by framework, service, or API gateway, so cross-check your environment's logs, trace IDs, and stack traces to map the failure to a specific code path. In practice, treating 3 245 as a server-side symptom helps you focus on the correct subsystem—whether it's authentication, validation logic, or a dependent service—and prevents chasing unrelated client behavior. Why Error Code emphasizes the need to correlate locally with your deployment history and telemetry before applying patches.
Symptoms you may see
Users experience intermittent 500 errors or failed API responses. You might notice repeated 3 245 entries in your server logs, a spike in latency just before the failure, or a sudden drop in downstream service health indicators. In distributed systems, the error can appear at a gateway or edge service even when the root cause lies deeper in the call chain. The Why Error Code approach of correlation between logs, metrics, and traces is essential here to determine whether the problem stems from permissions, input data, or a broken dependency.
Causes and how likely they are (prioritized)
- Invalid or expired credentials/permissions: high
- Input validation failure at the endpoint: high
- Misconfigured dependency (database, cache, message broker): medium
- Business-rule enforcement triggering a hard stop: medium
- Transient network or timeout in a downstream service: low
Context matters: a recent deploy or config change can flip the likelihood of these causes quickly. Always start with the most probable culprits that directly relate to the request handling path.
Quick fixes you can try now
- Restart the affected service or container to clear transient state. This is often the fastest way to verify if the problem is a momentary glitch.
- Roll back the most recent deploy or configuration change if the issue started after a release. If rollback fixes the problem, document the root cause for future fixes.
- Validate the incoming request against the API schema and business rules. Ensure required fields are present and correctly formatted. If you identify a problematic payload, implement a safer fallback or input sanitation.
- Check authentication tokens, scopes, and permissions tied to the operation. A missing or expired token can trigger server-side rejection that manifest as 3 245.
Deeper investigation (if quick fixes fail)
If the error persists after the quick fixes, turn to a structured diagnostic approach: isolate the function or service responsible, collect end-to-end traces, and reproduce in a staging environment with the same data shape. Use feature flags and targeted logs to narrow the failing path without flooding your production logs. This method reduces blast radius while preserving uptime for users.
Safety, monitoring, and when to call a pro
Only perform changes in a controlled window and ensure backups are available. If the issue involves sensitive data, regulated workflows, or hardware dependencies, escalate to a senior engineer or on-call expert. When in doubt, contact your on-call team and consider a professional assessment if the root cause lies beyond simple configuration or code fixes.
Prevention and resilience
Implement robust input validation, consistent error handling, and detailed telemetry so future 3 245 occurrences are easier to diagnose. Use automated tests that reproduce edge cases and add health checks that surface misconfigurations before they impact users. Maintain clear rollback procedures and keep dependencies up to date to reduce the chance of regression.
Steps
Estimated time: 60-90 minutes
- 1
Reproduce the error in a controlled environment
Capture a minimal, reproducible payload that triggers 3 245. This helps you isolate whether the issue is data-specific or a general path failure.
Tip: Use a sanitized test dataset to avoid leaking real data. - 2
Check logs and traces for the failing path
Search for the exact endpoint and function in the trace to identify where processing stops. Note the timestamps and correlation IDs.
Tip: Enable or access structured logs to improve searchability. - 3
Validate inputs and permissions at the boundary
Confirm that the request payload meets the required schema and that the caller has necessary permissions for the operation.
Tip: Add explicit validation errors to distinguish data issues from permission issues. - 4
Inspect dependencies and configuration
Check database connections, caches, or downstream services that the operation relies on. Look for timeouts or misconfigurations.
Tip: Verify environment variables and connection strings against the latest config. - 5
Apply a targeted patch or rollback if needed
If a recent change caused 3 245, either revert the change or patch the faulty logic with a safe fallback.
Tip: Keep a changelog of fixes for future root-cause analysis. - 6
Test end-to-end and monitor
Run end-to-end tests to confirm the issue is resolved, then watch live traffic and metrics to ensure stability.
Tip: Set temporary alerts to catch reoccurrence quickly.
Diagnosis: User API requests intermittently fail with backend error code 3 245 and service logs show a server-side failure during a critical operation
Possible Causes
- highInvalid/expired credentials or missing permissions
- highInput data failing endpoint validation
- mediumMisconfigured dependency (DB, cache, or downstream service)
Fixes
- easyRestart the affected service to clear transient state
- easyRoll back the most recent deployment or configuration change
- mediumAudit and fix API input validation and permissions for the endpoint
Frequently Asked Questions
What does backend error code 3 245 mean?
Backend error code 3 245 indicates a server-side failure during a critical operation, often due to validation or permission issues. It requires examining server logs and trace data to identify the failing component.
Backend error code 3 245 is a server-side failure during a critical operation, usually tied to validation or permissions.
Is 3 245 always a critical error?
Not always. It signals a server-side stop in processing, but the impact depends on the endpoint and the surrounding architecture. It should be treated promptly but investigated carefully to avoid unnecessary fixes.
It's serious but may vary in impact; investigate promptly to find the exact cause.
What should I check first when I see 3 245?
Begin by validating the request payload, credentials, and permissions for the endpoint. Then inspect recent deployments for changes that could affect the processing path.
Check input data, permissions, and recent changes first.
Can I fix 3 245 myself, or should I call a professional?
If you have access to logs, traces, and the affected code, you can attempt safe quick fixes like restarts and input validation checks. For complex dependencies or production-grade fixes, involve a senior engineer or on-call professional.
You can try safe, quick fixes if you know the system; otherwise call a pro.
Are there cost considerations for fixing 3 245?
Costs vary widely by environment, hardware, and labor. A professional assessment can add to the budget, but fixes implemented promptly can prevent larger downtime costs.
Costs vary; faster remediation often minimizes downtime costs.
How can I prevent 3 245 in the future?
Implement strict input validation, robust error handling, and comprehensive telemetry. Add automated tests for edge cases and maintain a reliable rollback and rollback-testing process.
Prevent it with validation, monitoring, and good rollback practices.
Watch Video
Top Takeaways
- Understand 3 245 as a server-side failure signal.
- Start with fast restarts and validations before deep debugging.
- Correlate logs, traces, and deployments to identify root cause.
- Monitor after fixes to ensure stability and prevent recurrence.