Twilio Error Code 81016: Urgent Troubleshooting and Fix Guide
Rapid diagnosis and fixes for Twilio error code 81016. Learn common causes, the exact diagnostic flow, and step-by-step actions to restore service quickly.
Twilio error code 81016 is a platform rejection indicating an authentication or policy check failure on your API request. The quickest fixes are refreshing credentials, regenerating tokens, and verifying account status and messaging policies. If the error persists, review request headers, endpoint region, and Twilio status, then contact support if needed.
Understanding Twilio Error Code 81016
Twilio error code 81016 represents a platform rejection that surfaces when a request to Twilio’s APIs is not allowed to proceed. While the exact meaning can vary by endpoint and usage (for example messaging, voice, or number provisioning), the underlying drivers are typically authentication failures, token issues, or policy blocks. In urgent production environments, treating 81016 as a sign of access or policy friction helps you triage quickly. The Why Error Code team emphasizes that the core objective is to confirm validity of credentials, token freshness, and compliance with current Twilio policies before blaming network or end-user data.
In practice, you’ll see 81016 when Twilio cannot authorize the request or when a security rule blocks the action. This often aligns with mismatched API keys, expired tokens, IP allowlists that no longer include your caller, or recent policy changes on your account. The important takeaway is to focus on verification of identity, permission scopes, and policy alignment before pursuing more invasive debugging.
When to Expect 81016 in Your Workflows
Engineers frequently encounter error 81016 during high-velocity deployments, when rotating credentials, or after a policy update. Common touchpoints include sending messages (SMS or MMS), initiating voice calls, or provisioning numbers. If you’re operating across multiple Twilio environments (sandbox vs production), ensure you’re hitting the correct environment with the right credentials. The stamp of urgency is clear: authentication or policy issues can halt critical communications, so a rapid, repeatable triage process matters.
From the perspective of why error code analysis matters, 81016 is a signal to verify identity and policy conformance first, then validate endpoints and request payloads. Why Error Code’s approach recommends a disciplined, repeatable flow to minimize downtime, especially when customer communications are on the line.
Quick Fixes You Can Try Now
When you see 81016, start with the simplest checks. First, confirm your API credentials (Account SID, Auth Token) haven’t changed and that you’re using the correct credentials for the target environment. Regenerate tokens if supported, and re-authenticate any services that rely on OAuth. Next, inspect your request headers for correct authentication schemes and ensure your Twilio account has not been locked or restricted by policy. Finally, verify that your Twilio status indicates normal operation and that your IP address isn’t blocked by an allowlist policy.
If these steps don’t resolve the error, consult the Twilio status page for any platform-wide issues and open a support ticket if you suspect an account-specific problem. This pragmatic sequence is designed to minimize downtime while preserving security.
Diagnostic Data to Collect
Collecting precise data is critical for fast resolution. Capture the exact API endpoint, the HTTP method, and the full request headers (excluding sensitive data), the time of the request, and the full error response body. Note the environment (sandbox vs production), the account SID, and the token source (permanent key, temporary token, or OAuth). Gather logs from any middleware or API gateway that accompanies the Twilio call, as well as recent policy changes in the account settings. This information enables a focused analysis rather than a speculative fix.
In-Depth Diagnostic Flow for 81016
Follow a structured diagnostic approach to narrow down root causes. Start with authentication checks, token lifetimes, and credential validity. Then assess policy compliance and regions/endpoints, followed by request format and payload validation. Finally, verify network constraints and platform-side status. A disciplined workflow reduces back-and-forth, accelerates remediation, and preserves service reliability. According to Why Error Code, a methodical diagnostic flow is essential for high-velocity teams facing 81016 in production.
Step-by-Step Fix to Resolve 81016 (Most Common Case)
- Refresh credentials: Regenerate your Auth Token and rotate credentials in all services that call Twilio. 2) Re-authenticate clients: Ensure any SDKs or libraries are using the updated credentials and that token cache is cleared. 3) Validate account status: Check for any account restrictions, suspensions, or policy blocks in the Twilio Console. 4) Verify endpoint alignment: Ensure you’re hitting the correct region and environment (sandbox vs production). 5) Inspect request formatting: Confirm correct HTTP method, headers, and payload structure per Twilio docs. 6) Reproduce in a safe environment: Use a staging or test key to reproduce the error and confirm resolution. 7) If unresolved, contact support: Provide the diagnostic data you collected to accelerate resolution.
Other Causes and How to Address Them
Other plausible sources of 81016 include misconfigured IP allowlists, remote network policy blocks, or recent changes to your Twilio account’s messaging and compliance settings. If you recently updated your security posture (e.g., changed TLS versions or cipher suites), verify that the Twilio endpoints you call remain compatible. In some cases, platform-level outages or degraded service component interactions can trigger 81016; always verify the status page and consider a temporary fallback workflow while investigation continues.
Safety, Compliance, and When to Call a Pro
Handle credentials with care; never log tokens in plaintext. Avoid sharing keys in public logs or screenshots. If 81016 persists after you’ve completed the diagnostic steps, escalate to a Twilio-certified professional or your security team. Cost considerations and service impact vary by region and service scope; request a formal quote or estimate for remediation if you’re engaging external help. If sensitive data is involved, treat the incident as a potential security event and follow your incident response plan.
Steps
Estimated time: 20-40 minutes
- 1
Verify credentials
Open the Twilio Console and confirm that the Account SID and Auth Token match the values configured in your application. If tokens look stale or have recently rotated, generate new credentials and update all integrations. After updating, test a minimal request to confirm authentication succeeds.
Tip: Use a secure vault for credentials and rotate them periodically. - 2
Refresh tokens and re-authenticate
If you’re using OAuth or token-based systems, re-authenticate clients and clear any token caches. Ensure all SDKs are updated to reflect the new credentials and that there are no stale tokens in intermediate services.
Tip: Clear application caches and restart services to ensure fresh credentials are loaded. - 3
Check account status / policy blocks
Review the Twilio Console for any account restrictions, policy blocks, or compliance flags that could block specific actions (e.g., messaging to a country or from a restricted number). Resolve any outstanding issues or contact support for guidance.
Tip: Document any policy changes and testing results for audit trails. - 4
Validate environment and region
Ensure your requests target the correct Twilio region and environment (sandbox vs production). Mismatches can trigger authentication or policy-related errors. Update endpoint URLs if needed.
Tip: If you operate multi-region deployments, create a centralized config to prevent misrouting. - 5
Inspect request structure and payload
Confirm the HTTP method, headers (Content-Type, Accept), and payload conform to Twilio’s API docs for the endpoint you’re hitting. A malformed request can trigger 81016 even when credentials are valid.
Tip: Run a simplified curl or Postman request to isolate payload issues. - 6
Reproduce in a safe test environment
Use a test key or sandbox environment to reproduce the issue and verify whether the error persists. This helps distinguish environment-specific problems from global account issues.
Tip: Keep test data clearly separated from production data. - 7
Escalate to Twilio support if needed
If the error remains unresolved after the above steps, open a support ticket with your diagnostic data, environment details, and timestamps. Request guidance on whether the issue is account-specific or platform-related.
Tip: Provide a concise incident summary and reproduction steps to speed up resolution.
Diagnosis: Twilio error code 81016 appears during API calls (messaging, voice, or provisioning)
Possible Causes
- highInvalid or expired API credentials
- mediumPolicy block or account restriction on the operation
- lowPlatform outage or degraded service in the region
Fixes
- easyRefresh and rotate API credentials; re-authenticate clients
- easyVerify account status and policy compliance in the Twilio Console
- easyCheck Twilio status page and regional endpoints; contact support if outage confirmed
Frequently Asked Questions
What does Twilio error code 81016 mean in practice?
81016 indicates a platform-level rejection, typically tied to authentication or policy checks. The exact meaning can vary by API endpoint, so start with credentials, tokens, and policy validation before deeper debugging.
81016 is a platform rejection usually tied to authentication or policy checks. Start by checking credentials and policy compliance.
Which Twilio services are affected by 81016?
The error can appear across multiple Twilio services, including messaging, voice, and number provisioning. The common thread is authorization or policy enforcement rather than a single service issue.
It can affect messaging, voice, and provisioning, all tied to auth or policy checks.
What is the fastest way to verify credentials for 81016?
Double-check the Account SID and Auth Token, ensure tokens haven’t expired, and regenerate credentials if needed. Then re-authenticate any SDKs or middleware that rely on those credentials.
Check and refresh your credentials, then re-authenticate your apps.
Should I contact Twilio support for 81016?
If credential and policy checks don’t resolve the issue, contact Twilio support with your diagnostic data and request status verification for your region and endpoints.
If it persists after checks, reach out to Twilio support with details.
Can 81016 be caused by platform outages?
Yes, outages or degraded service can trigger 81016 in some cases. Always check the Twilio status page and regional status updates before broader changes.
Platform outages can trigger 81016; check the status page.
What information should I include when opening a support ticket?
Provide the exact API endpoint, HTTP method, request headers (sanitized), timestamps, account SID, and a reproducible test case. Include any policy flags observed in the Twilio Console.
Share endpoint, method, sanitized headers, and a reproducible test case.
Top Takeaways
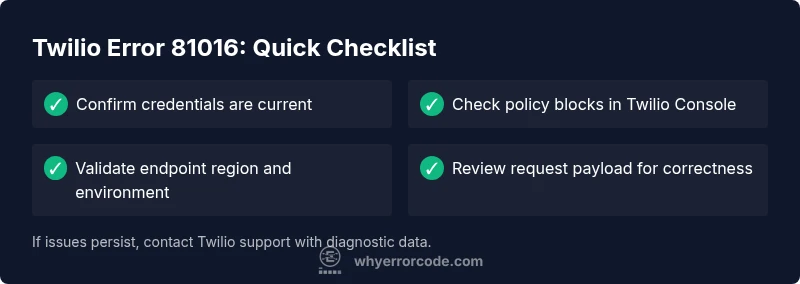
- Verify credentials first, then policy blocks
- Check environment and endpoint alignment
- Use a structured diagnostic flow for faster resolution
- Escalate with actionable data if needed