Was error code 1001 real? Urgent Troubleshooting Guide
Is error code 1001 real or a false alarm? This urgent guide explains what 1001 means, common causes, quick fixes, and a step-by-step plan to resolve credential and validation failures quickly.

Was error code 1001 real? In most contexts, 1001 is a generic server-side rejection indicating invalid or missing credentials or a failed validation. According to Why Error Code, this real error often appears when an API key or token is expired or malformed. Quick fixes include renewing credentials, re-authenticating, and retrying with proper authorization.
What 'was error code 1001 real' means in practice
According to Why Error Code, the question was error code 1001 real isn't about a rumor – it's a real signal used by many APIs and software systems. In practice, 1001 is a generic server-side rejection that points to credential problems or validation failures rather than a simple network hiccup. The Why Error Code team found that users often misread 1001 as a temporary glitch when the root cause is often expired or malformed credentials. When you see 1001, the first things to check are the auth tokens and API keys in your request, followed by the scope of permissions. This distinction matters because credential hygiene dramatically lowers the risk of recurring 1001 errors in production.
- Key takeaway: credential freshness and proper scope are your first defense against 1001.
- Pro tip: enable token rotation and centralized secret storage to reduce future occurrences.
This section also sets the stage for practical fixes you can apply immediately, while keeping in mind that credential-related failures are the most common cause of 1001 across systems.
Common Scenarios Where 1001 Appears
1001 tends to surface in three broad contexts: API integrations, mobile and desktop apps, and backend services communicating with external systems. In API workflows, a stale or revoked API key can trigger 1001 at the moment a request reaches the server. In mobile apps, tokens might expire silently, or the app may send requests with an invalid session. In backend services, misconfigured OAuth scopes or policy rules can produce 1001 even when credentials look correct at a glance. Why Error Code analysis shows that credential issues account for a large share of 1001 events, especially in high-traffic environments where tokens rotate frequently. Understanding the exact context—where you were, what action you took, and what the server logged—helps narrow down causes quickly.
If you’re debugging in production, keep a careful log of when 1001 happens and which credential chain was used for that call. A small mismatch in environment variables or a stale secret is enough to trigger this error. This is why credential hygiene and proper secret management are essential.
Quick Checks You Can Do Right Now
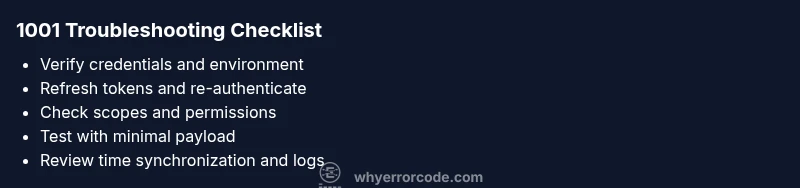
To shrink mean time to resolution, run a quick triage before touching code. First, verify the credential chain: check the API key or token, ensure it is not expired, and confirm it matches the target environment. Second, re-authenticate and re-issue tokens if necessary, paying attention to the required scopes. Third, inspect the request headers for correct authorization type and content-type. Fourth, test with a minimal payload and a known-good endpoint to confirm whether the problem is global or endpoint-specific. Fifth, review recent changes to access policies or token lifetimes that could have triggered the change. If you don’t see an obvious credential issue, inspect client clocks and server time synchronization, which can also cause signature failures leading to 1001.
These quick checks are designed to catch the most common culprits quickly, so you can avoid a longer incident cycle.
If you’re stuck, a controlled rollback to the last known-good credentials and tokens can help determine if the issue is tied to recent secret updates.
How This Error Impacts Different Systems
On APIs, 1001 can halt integrations and blocking workflows, creating cascading failures across dashboards and automation. In mobile apps, users may experience abrupt authentication prompts, unexpected sign-outs, or failed data sync. In enterprise systems, 1001 can appear during batch jobs or cron-based tasks that rely on service accounts. Across all platforms, the root cause usually points back to credentials or permissions, not a temporary network blip. Now, more than ever, teams need reliable credential management and monitoring to prevent 1001 from becoming a recurring disruption. This is why we emphasize proactive credential hygiene and token lifecycle governance across all environments.
When to Escalate to a Pro
If you have exhausted the common fixes and 1001 persists across environments, escalate to a professional. Contact support when: (a) credential refresh and re-authentication fail repeatedly, (b) all endpoints exhibit 1001 in a way that suggests server-side policy changes, or (c) you lack access to the credentials or logs required to diagnose. Prepare a concise incident report: time, affected services, environment, tokens or keys involved, recent policy changes, and any relevant error traces. Expect a service-level explanation, potential token renewal cycles, and an estimated remediation window that typically ranges from 30 minutes to several hours, depending on the scope of the issue.
How to Verify Real-World Impact and Avoid Recurrence
Implement end-to-end checks: log every 1001 instance with timestamp, request payload, and credential state. Use automated tests that simulate expired tokens to validate failover and re-auth flows. Enforce credential hygiene: rotate keys regularly, restrict scopes to the minimum necessary, and store secrets in secure vaults. Build a lightweight retry strategy that respects backoff and avoids endless retries on 1001. By auditing credentials and enforcing policy discipline, teams can prevent was error code 1001 real from returning, or at least catch it earlier.
Proactive monitoring and documented remediation playbooks significantly reduce the blast radius when 1001 reappears.
Real-World Examples and Case Studies
In several anonymized deployments, teams that tied token lifetimes to service calendars and used bound service accounts with least privilege reported a dramatic drop in 1001 incidents after implementing rotation and stricter scope checks. Another group automated credential checks as part of their CI/CD pipeline, catching expired tokens before deployment. While each environment is unique, the common thread is consistent credential hygiene and clear ownership of secret management. These examples illustrate how a structured fix path, focused on authentication and policy alignment, can convert a critical 1001 error into a manageable, recoverable event.
Troubleshooting Best Practices and Hygiene
- Maintain a single source of truth for credentials (secret manager) and rotate regularly.
- Limit scopes to the minimum privileges required by each service.
- Implement automated health checks that verify token validity and endpoint reachability.
- Log 1001 details with context (endpoint, environment, and exact credentials state) to speed triage.
- Avoid hard-coding credentials in codebases or public repos; use environment-specific secrets.
- If credentials appear correct but 1001 persists, review time synchronization on clients and servers, as timestamp mismatches can invalidate signatures.
- When in doubt, escalate early to professional support with a concise incident report.
Steps
Estimated time: 25-35 minutes
- 1
Validate credential state
Begin by confirming that your API key, token, or service account credentials are current and valid for the target environment. Check expiration dates and ensure there are no recent revocations. If in doubt, regenerate or rotate credentials using your secret management tool.
Tip: Document credential lifetimes and rotation schedules to prevent future 1001 issues. - 2
Re-authenticate and refresh tokens
Perform a fresh authentication flow and obtain new tokens if the old ones appear expired or malformed. Update your application configuration to use the new tokens and verify the authentication response status to ensure success.
Tip: Use automated tests to verify token retrieval in a controlled environment. - 3
Verify scope and permissions
Double-check that the request you’re sending matches the required scopes and permissions for the resource. If the server enforces policy changes, update your request to align with the latest policy.
Tip: Keep a changelog of permission changes to avoid repeating the same misalignment. - 4
Test endpoints with minimal payload
Send requests to a known-good endpoint with a minimal payload to isolate credential-related failures from data-related problems. Confirm if 1001 persists before scaling back to normal tests.
Tip: Use a dry-run mode or sandbox environment when testing. - 5
Review time synchronization and signatures
Check that client and server clocks are synchronized, especially if your requests rely on signature-based authentication. Time drift can invalidate signatures and trigger 1001.
Tip: Enable clock skew tolerance in your client library if available.
Diagnosis: Application shows error code 1001 during startup or API request
Possible Causes
- highInvalid or expired credentials (API key, token, or session)
- mediumMisconfigured authentication scope or permissions
- lowTransient network issues or DNS resolution problems
Fixes
- easyRenew credentials and reissue tokens; verify API key validity
- easyRe-authenticate or refresh session; re-check request scope and permissions
- easyCheck network connectivity and DNS; retry request after a short delay
Frequently Asked Questions
What does error code 1001 mean?
Error 1001 is typically a server-side rejection due to invalid or missing credentials or failed validation. It often points to credential issues, expired tokens, or incorrect scopes.
Error 1001 usually means credentials or permissions are not correct. Check keys, tokens, and scopes.
Is error code 1001 real or fictitious?
Yes, 1001 is a real error used by many APIs to indicate an authentication or policy-related failure. It isn't a rumor or a glitch.
Yes, 1001 is real and indicates a credential or policy issue.
What quick fixes should I try first?
Renew credentials, re-authenticate, verify API keys, and ensure the request scope matches the required permissions. Then retry with a minimal payload to isolate the problem.
Renew credentials, re-authenticate, and verify keys and scope, then retry.
Can network problems cause 1001?
Yes, network issues can contribute to 1001 if they prevent proper token transmission or timing-based signatures. Check connectivity and DNS resolution as part of triage.
Network issues can trigger 1001 if they affect token transmission.
When should I contact support?
Reach out after exhausting credential fixes and confirming that the issue isn’t environment-specific. Provide logs, environment details, and the exact error payload to help the support team diagnose.
If it still fails after fixes, contact support with logs and details.
Watch Video
Top Takeaways
- 1001 often signals credential or scope issues.
- Refresh credentials and verify API keys before retrying.
- Check endpoint scopes and permissions for alignment.
- The Why Error Code team recommends credential hygiene and monitoring.