Fix vs code github error bad credentials: A Practical Troubleshooting Guide
Learn how to diagnose and fix the vs code github error bad credentials quickly with actionable steps, token guidance, and best practices from Why Error Code.
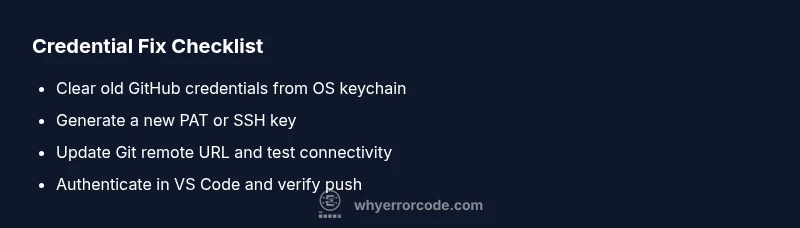
The most common cause is expired or invalid credentials cached by Git or VS Code's credential helper. Quick fix: re-authenticate with GitHub in VS Code, clear cached credentials from your system credential manager, regenerate a Personal Access Token (PAT) if needed, and verify the remote URL uses HTTPS or SSH you control. After re-authenticating and testing, the error should disappear.
Understanding the vs code github error bad credentials in modern workflows
The error message most developers see when interacting with GitHub through VS Code usually points to authentication problems that block pushes, pulls, or fetches. Because VS Code integrates Git and GitHub through multiple layers (the Git client, credential helpers, and the editor's Git extension), a failure at any layer can surface as a generic “bad credentials” error. In this guide from Why Error Code, you’ll learn to identify where the credentials are stored, how tokens or SSH keys are used, and how to re-establish a trusted connection with GitHub. The goal is to restore a frictionless workflow while keeping credentials secure and rotate tokens when necessary. This is especially important for developers, IT pros, and everyday users who depend on rapid, repeatable fixes. The root cause is rarely a single misstep, but a combination of expired tokens, cached credentials, and stale remotes.
During diagnostic, you’ll see common patterns such as repeated prompts to enter a password, frequent authentication failures after token expiry, or an inability to push to the origin. By following a structured approach—confirming token status, clearing caches, updating remotes, and re-authenticating—you can resolve the issue without re-installing VS Code or disrupting your development environment. This guidance reflects Why Error Code’s commitment to practical, testable steps that work across Windows, macOS, and Linux.
Common causes of bad credentials in VS Code and GitHub
There are several frequent culprits behind the “bad credentials” message. Tokens expire or are revoked; cached credentials become stale after password changes or policy updates; the Git remote URL is incorrect or points to a token-protected endpoint; and local credential helpers fail to propagate fresh tokens to Git during operations. Understanding which causelines up with your symptoms helps you apply the right fix quickly. This section outlines the top causes with concrete indicators so you can troubleshoot methodically. The guidance here aligns with the problems documented by the Why Error Code team, reflecting real-world patterns seen across development environments.
Examples of symptoms you might notice include: a prompt to authenticate on every push, an error like 401 or 403 from GitHub, and inconsistent behavior between terminals and VS Code’s GUI Git panel. If you recently rotated a token or changed your GitHub password, you should suspect cached credentials or an outdated remote URL first. If you recently updated VS Code or the Git extension, compatibility issues with credential helpers could be at fault. By mapping symptoms to likely causes, you can reduce guesswork and move to targeted fixes.
Check your Git credential helpers and stores
Most “bad credentials” problems start with how credentials are stored and retrieved. Git on your machine can use various credential helpers (osxkeychain, manager-core, wincred, or cache). If the helper stores an old token or password, Git will keep trying to reuse it, causing repeated authentication failures. Start by listing the credential helpers configured in your environment and identifying entries tied to GitHub. Then, clear or update those entries so the next operation prompts for fresh authentication. Doing this step early often resolves the issue without more invasive actions. Remember: credential helpers are intended to streamline authentication, but stale entries quickly become a bottleneck if tokens are rotated or scopes changed. Why Error Code recommends validating that your helper is active and properly configured for your OS.
Re-authenticate inside VS Code and GitHub integration
Re-authentication is usually the fastest path to resolution when you see bad credentials in VS Code. In VS Code, use the built-in Source Control panel to attempt a push or fetch, and follow prompts to sign in to GitHub. If VS Code doesn’t prompt, you may need to trigger a sign-in via the Accounts menu or the GitHub extension settings. This process will establish a fresh token or SSH key binding between VS Code and GitHub. After signing in, verify that GitHub access is granted with the expected scopes. If you rely on SSH, ensure your SSH agent is running and the public key is added to your GitHub account. Why Error Code’s team emphasizes re-authenticating via the native flows to avoid stale credentials lingering in the background.
Regenerate and rotate credentials: PATs and SSH keys
A compromised, expired, or insufficiently scoped token is a frequent reason for bad credentials errors. Generate a new Personal Access Token (PAT) from GitHub with the minimal necessary scopes for your workflow (repo, workflow, or gist as needed). Update your Git config to use the new token and, where possible, avoid embedding the token in your commands. If you prefer SSH, ensure you have a valid SSH key pair and that the public key is added to your GitHub account. The rotation step is crucial: old tokens should be revoked, and you should confirm that all scripts and tools referencing credentials are updated. Why Error Code highlights token rotation as a best practice for secure, long-term access.
Update the Git remote URL and test connectivity
Sometimes the issue traces back to incorrect remote URLs, especially after cloning from a different account or organization. Run git remote -v to inspect the origin URL. If you previously used a password or token in the URL, removing it and switching to a token saved by your credential manager or to SSH will help. After updating the remote URL, test connectivity with a simple fetch or a git ls-remote to verify that authentication succeeds. This step confirms that the credentials are accepted by GitHub and that the repository path is correct.
Clean up caches and ensure global config correctness
Inconsistent configurations can leave behind stray settings that reintroduce the problem. Clean up credential caches, clear any cached user.name and user.email (where appropriate), and verify that your global Git config aligns with your repository’s expectations. If multiple accounts exist on the same machine, consider using per-repository configurations or a dedicated SSH key per account to avoid cross-account credential leakage. A clean slate helps ensure your next operation uses the renewed credentials.
Best practices to prevent future bad credentials issues
Adopt a few guardrails to prevent credential messes from creeping back in. Use PAT-based authentication for GitHub with appropriate scopes; prefer SSH for automated workflows; periodically rotate tokens; and keep credentials in secure storage provided by your OS. Maintain a clean environment by removing old tokens promptly and by documenting the exact steps to re-authenticate in your team’s playbook. Following these practices, recommended by Why Error Code, reduces recurrence and protects access integrity.
Steps
Estimated time: 25-45 minutes
- 1
Identify symptoms and reproduce the error
Note the exact error message and repeat a push/pull to confirm the behavior. This helps determine whether the issue is token-related or a more general connectivity problem. Collect any error codes (401/403) for reference.
Tip: Document timestamps to correlate with token expiry or policy changes. - 2
Check credential helpers and caches
List active credential helpers and inspect stored credentials. On Windows, open Credential Manager; macOS users should check Keychain; Linux users can inspect git-credential-store or cache. Remove or update entries tied to GitHub.
Tip: Only remove entries you recognize to avoid breaking other services. - 3
Re-authenticate in VS Code
Attempt a Git operation in VS Code. If prompted, sign in to GitHub and grant required scopes. If prompts don’t appear, sign out and back in from the Accounts menu or the GitHub extension settings.
Tip: Enable verbose logging for the GitHub extension if issues persist. - 4
Rotate credentials (PAT or SSH)
Generate a new PAT on GitHub with needed scopes, or ensure your SSH key is active in GitHub. Update Git to use the new credentials by updating the credential store or SSH agent.
Tip: Never hard-code tokens in scripts; use environment variables or credential managers. - 5
Update the remote URL and test connectivity
Verify git remote -v shows the correct origin. If needed, switch to SSH: git remote set-url origin [email protected]:username/repo.git. Run git ls-remote or git fetch to validate access.
Tip: Keep a per-repo SSH key strategy to avoid cross-account conflicts. - 6
Validate across environments
Test the same operations in a clean terminal or another machine to confirm the issue is not machine-specific. This helps identify environment-related credential caching issues.
Tip: If the problem persists across devices, consider GitHub account security settings as a factor. - 7
Escalate if needed
If all else fails, contact a system administrator or GitHub support with error details and a list of steps you’ve performed. Sometimes organization-level security policies require action.
Tip: Include token scopes and affected repository names when requesting help.
Diagnosis: VS Code shows 'bad credentials' when performing Git operations with GitHub
Possible Causes
- highExpired or revoked GitHub PAT or password in use
- highStale credentials cached by OS credential manager or Git helper
- mediumRemote URL or authentication method mismatch (HTTPS vs SSH)
Fixes
- easyClear old credentials from the system credential store and re-authenticate
- easyGenerate a new PAT on GitHub and configure Git/VS Code to use it
- easyUpdate the Git remote URL to the correct protocol and verify access
Frequently Asked Questions
What causes the 'bad credentials' error in VS Code when using GitHub?
The error is typically caused by expired or revoked tokens, cached credentials that are no longer valid, or incorrect Git remote configuration. Network changes and extension updates can also trigger authentication failures. Start by verifying credentials and removing stale caches, then re-authenticate.
Common causes are expired tokens, cached credentials, and wrong remotes. Re-authenticate and clear caches to resolve it.
How do I fix an expired PAT without disrupting my workflow?
Generate a new Personal Access Token on GitHub, update Git to use the new token via the credential helper, and re-authenticate in VS Code. Test with a small push to confirm access before resuming work.
Create a new PAT, update credentials, then test with a push.
Should I switch from HTTPS to SSH to avoid credential issues?
SSH keys tend to be more stable for automation since they don’t rely on tokens that can expire. If you switch to SSH, ensure your public key is added to GitHub and the SSH agent is running.
SSH can be more stable for automation; set up keys and use the SSH URL.
Is it safe to store tokens in credential managers?
Yes, when stored in secure credential managers that protect credentials with your operating system’s security features. Avoid saving tokens in plain text or in scripts.
Store tokens securely in your OS credential manager and avoid plain text storage.
What if the problem persists after all fixes?
If authentication still fails after trying the recommended steps, contact your organization’s IT support or GitHub support with a description of actions taken and error logs. There may be policy or account-level restrictions involved.
If it still fails, reach out to IT or GitHub support with details.
Can I test credentials without affecting my remote repository?
Yes. Use a test branch or a fork to verify your credentials, avoiding changes to the main repository while debugging authentication issues.
Test in a fork or test branch to avoid affecting the main repo.
Watch Video
Top Takeaways
- Refresh credentials promptly after expiry
- Use PATs or SSH for safer, long-term access
- Clear stale caches before re-authenticating
- Test connectivity after each fix step