Remote Desktop Fatal Error Code 5: Immediate Diagnostic Guide
Learn how to diagnose and fix remote desktop fatal error code 5 quickly. This urgent guide covers symptoms, top causes, step-by-step fixes, safety tips, and when to call a professional from Why Error Code.

Remote desktop fatal error code 5 means the connection is blocked due to access permissions or security settings. Typical fixes include running the client with elevated privileges, ensuring the target host allows remote connections, and adjusting firewall rules. If still blocked, a professional might be needed. This guide explains how to diagnose the issue quickly and outlines safe, step-by-step fixes.
Symptom and Meaning
According to Why Error Code, remote desktop fatal error code 5 usually indicates a permissions or security restriction is blocking the connection. Users often see a message that the login attempt was denied or that the remote host refuses the session. This error is not exclusively a single cause, but a signal that one or more security layers are preventing access. The quickest path to resolution is to verify basic access rights first, then expand to host-level settings. Recognizing the exact meaning helps you prioritize fixes without wasting time on irrelevant adjustments.
A key aspect of the error is its dependency on both client and server-side configurations. If either side enforces stricter authentication, multi-factor prompts, or restricted user groups, the connection will fail with error code 5. In enterprise environments, network policies may also influence this outcome. By focusing on permissions and security posture first, you’ll often resolve the majority of cases with minimal downtime.
wordCountInBlockOnly":null}
Why This Error Happens in Modern Setups
Why Error Code analysis shows that remote desktop fatal error code 5 commonly stems from misconfigured permissions on either the local client or the remote host, combined with restrictive security policies. In single-user environments, a missing local account privileges can trigger the block. In corporate networks, domain policies, conditional access, and privilege elevation requirements frequently contribute to the symptom. The overarching lesson is: permission and security posture are the leading drivers behind error code 5.
From a troubleshooting perspective, you should confirm that the user account has permission to log in remotely and that the remote device accepts RDP connections. If group policy or local security policy prohibits remote logon, the error will appear even when basic network reachability is fine. The Why Error Code team emphasizes testing changes in small, reversible steps to avoid unintended exposure.
wordCountInBlockOnly":null}
Most Common Causes (Ranked)
- Permission gaps on the remote machine (high likelihood): The most frequent root cause is that the user account attempting the connection does not have the required remote login rights or the remote session is blocked by local policies. This is the primary suspect in many environments.
- Firewall or network filtering (medium likelihood): A firewall on either side or a network security appliance may block the RDP traffic or disrupt authentication handshakes. Ensure port 3389 is allowed for the remote host and that VPNs or proxies aren’t interfering.
- Group Policy or registry restrictions (low likelihood): In some cases, misconfigured policies or registry entries prevent remote logon. This is less common but can be tricky to diagnose if you’re not familiar with policy scopes.
- Credential or multi-factor issues (low to medium): Expired passwords, device trust failures, or MFA prompts that cannot be fulfilled can appear as a code 5 block when authentication cannot complete.
- Remote host health and service status (low likelihood): If the Remote Desktop Services service on the target is stopped or degraded, you may encounter access troubles that manifest as a code 5 in some clients.
wordCountInBlockOnly":null}
Quick Fixes You Can Try Right Now
- Run the RDP client as administrator to ensure sufficient privileges for authentication and session creation. This is a quick, low-friction step that resolves many permission-related blocks.
- Verify that the remote host is configured to allow remote connections and that the user is a member of the Remote Desktop Users group or has equivalent privileges.
- Check the local and remote firewall settings to confirm that port 3389 (TCP) is open for both inbound and outbound traffic. Disable temporarily only if you understand the security implications and re-enable after testing.
- Review basic network connectivity (ping or traceroute) to ensure there is no obstruction between client and host. If you’re using VPNs, verify that the VPN policy permits RDP traffic.
- If you’re on a corporate network, request a temporary exception from the security team or IT admin while you test fixes. Always document changes for future reference.
wordCountInBlockOnly":null}
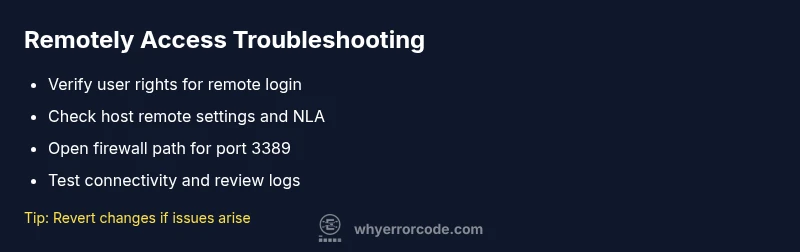
Step-by-Step Fix for the Primary Cause (Permissions on Remote Host)
Step-by-Step Fix: Target the Remote Host Permissions (1)
- number: 1 title: Verify Remote Desktop Access Rights description: Confirm the user account is granted Remote Desktop User rights on the target machine and that there are no Deny logon restrictions for the account or group. If needed, add the user to the Remote Desktop Users group and remove any explicit Deny logon rights. tip: Always perform changes with an administrator account and test with a non-critical user first.
- number: 2 title: Check Local Security Policy and Group Policy description: Inspect the Local Security Policy (secpol.msc) and any applicable Group Policy Objects to ensure there are no restrictions on logon through Remote Desktop. Enable “Allow log on through Remote Desktop Services” for the relevant user or group. tip: When in doubt, revert policy edits to known-good baselines before re-testing.
- number: 3 title: Validate Network Level Authentication (NLA) description: If NLA is enforced, ensure the client presents valid credentials and that the remote host supports NLA for all accounts. Disable NLA only if you understand security implications and you have alternative protections in place. tip: If you disable NLA, monitor access logs closely for unusual login activity.
- number: 4 title: Test with a Local Admin Account description: Try connecting with a local admin account to confirm whether the issue is account-specific. If the local admin works, compare permissions between the accounts to identify gaps. tip: Document differences in permissions to inform future user provisioning.
- number: 5 title: Reattempt Connection and Verify Event Logs description: After applying permissions, attempt the connection again and review Event Viewer logs on both client and host for authentication-related events. Look for IDs related to logon failures or policy enforcement. tip: Use filtered views to focus on Security and System logs during testing.
estimatedTime":"45-90 minutes"}
Other Causes and How to Fix Them
Other Causes and How to Fix Them (1)
- number: 1 title: Firewall Blocking RDP Traffic description: Ensure firewall rules allow TCP 3389 for both directions. Create explicit allow rules and test connectivity with a port-check tool. tip: If you’re unsure about firewall changes, test in a controlled lab environment first.
- number: 2 title: Network Policy or VPN Interference description: Some VPNs or network policies block RDP flows. Coordinate with network admins to open required paths or establish a secure RDP gateway. tip: Document VPN configurations to avoid repeating issues.
- number: 3 title: Invalid Credentials or MFA Hurdles description: Expired passwords or failing MFA prompts can surface as access blocks. Update credentials and ensure MFA prompts complete on both ends. tip: Rotate credentials securely and keep a recovery plan.
- number: 4 title: Remote Desktop Services State on Host description: Check that the Remote Desktop Services service is running on the host and that the host isn’t in a stale startup state. Restart services if necessary. tip: Schedule restarts during maintenance windows to minimize user impact.
wordCountInBlockOnly":null}
Safety, Warnings, and When to Call a Professional
Safety, Warnings, and When to Call a Professional (1)
- number: 1 title: Security First description: Do not disable security controls permanently. Document changes and ensure you revert any risky configurations after testing. tip: Use isolated test accounts when trying aggressive permission changes.
- number: 2 title: Backups Before Major Config Changes description: Always back up credentials, policies, and registry keys before applying significant changes. In corporate environments, obtain written change approvals. tip: Maintain a rollback plan with clear steps.
- number: 3 title: When to Involve IT Security or a Pro description: If changes affect multiple machines, involve IT security or a qualified professional to avoid broad exposure or policy violations. tip: A vetted professional can help map out a safe, auditable remediation path.
wordCountInBlockOnly":null}
Prevention Tips and Best Practices
Prevention Tips and Best Practices (1)
- number: 1 title: Document Permissions Baseline description: Create a baseline of permissions for all users who require remote access and review it quarterly. tip: Use a centralized IAM approach where possible.
- number: 2 title: Regular Policy Audits description: Schedule periodic checks of Local and Group Policy that affect Remote Desktop. Update in response to changes in roles and teams. tip: Automate policy checks where feasible.
- number: 3 title: Network Hygiene description: Keep systems updated, monitor for unusual login attempts, and maintain a secure perimeter around RDP endpoints. tip: Enable logging and alerting for failed logon events.
- number: 4 title: Least Privilege Principle description: Grant only the minimum privileges needed for remote access. Reassess privileges during audits to prevent privilege creep. tip: Proactively revoke unused accounts and permissions.
wordCountInBlockOnly":null}
Steps
Estimated time: 45-90 minutes
- 1
Prepare and Verify Credentials
Ensure you have administrative access on both client and host. Confirm the account is not disabled and that credentials are current. If MFA is required, verify that prompts can be completed.
Tip: Test credentials with a quick local login first to confirm basic access. - 2
Run RDP Client with Elevated Privileges
Right-click the Remote Desktop client and choose Run as administrator. This clears many permission-related blocks without modifying security policies.
Tip: Use a dedicated admin session for testing to avoid credential leakage. - 3
Enable Remote Desktop on the Host
On the host, open System Properties > Remote settings, and ensure 'Allow remote connections to this computer' is selected. Confirm the user group is allowed and that Network Level Authentication (NLA) settings match client capabilities.
Tip: If you’re in a domain, ensure the domain policy allows remote connections. - 4
Audit Firewall Rules for RDP
Check both client and host firewalls to ensure TCP 3389 is open. Add explicit allow rules if necessary and test connectivity with a port scanner.
Tip: Do not disable firewall entirely; constrain access to known networks or IPs. - 5
Test Connectivity and Review Logs
Attempt a new connection, then review Event Viewer on the host for logon failures (Security and System logs) and verify authentication events.
Tip: Document any error IDs to tailor the next steps.
Diagnosis: Remote Desktop fails to connect with error code 5
Possible Causes
- highPermission gaps on the remote machine (local user rights missing)
- mediumFirewall or network filtering blocking RDP traffic
- lowGroup Policy or registry restrictions preventing remote logon
Fixes
- easyVerify and grant Remote Desktop User rights on the remote machine; ensure login policies allow remote access
- easyOpen port 3389 in the firewall and verify inbound/outbound rules for RDP
- hardReview and adjust Group Policy/registry settings related to remote logon; if needed, revert to safe defaults
Frequently Asked Questions
What does remote desktop error code 5 mean?
It indicates a permissions or security block preventing the RDP connection. Check user rights, host settings, and firewall rules.
Error code 5 means your RDP connection is blocked by permissions or security settings.
Can I fix error 5 myself?
Often yes, by elevating privileges, adjusting host permissions, and validating network paths. If you’re on a corporate network, consult IT.
You can usually fix it yourself, but on work networks, check with IT.
Which ports should be opened for RDP on the firewall?
Port 3389 TCP is used by RDP; ensure inbound and outbound rules allow it on both client and host.
RDP uses port 3389; make sure it’s open through the firewall.
When should I contact a professional?
If policy changes risk security or affect many machines, or you’re uncomfortable editing registry or group policies.
Call a professional if changes risk security or affect multiple devices.
Do I need a license for Remote Desktop?
RDP involves licensing for certain editions and servers; verify your Windows edition and licensing requirements.
Licensing depends on your Windows edition; check your setup details.
Watch Video
Top Takeaways
- Identify the root cause: permissions first, then network blocks.
- Verify host acceptances: remote settings, group membership, and NLA alignment.
- Open and test RDP paths: firewall rules and network reachability.
- Consult IT security or a professional if changes impact many devices.