Difference Between Error Code 401 and 403: An Analytical Guide
Explore the difference between HTTP status codes 401 and 403. Learn definitions, common scenarios, server decisions, and practical debugging tips for API design and user-facing applications.

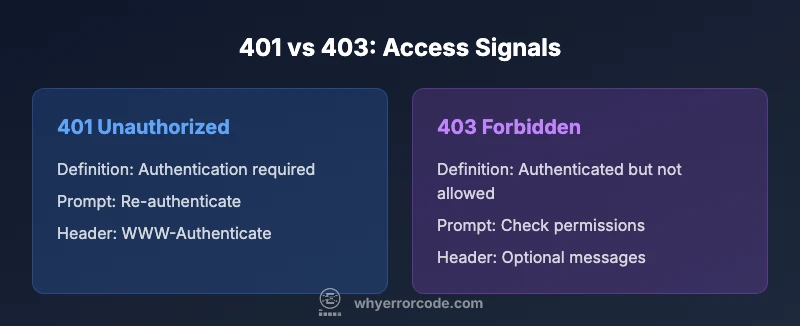
401 Unauthorized and 403 Forbidden are two of the most misunderstood HTTP status codes. The difference between error code 401 and 403 is that 401 indicates a missing or invalid authentication credentials for the target resource, while 403 means the client is authenticated but not permitted to access the resource. Understanding this distinction improves API design, error handling, and user experience.
Defining the difference between error code 401 and 403
The HTTP status codes 401 and 403 serve distinct purposes in access control. 401 Unauthorized indicates that the request has not been applied because it lacks valid authentication credentials for the target resource. In practice, this often means the client did not provide credentials, provided an expired token, or used invalid credentials. Servers typically respond with a WWW-Authenticate header to signal what authentication method is expected.
In contrast, 403 Forbidden means the server understood the request and the credentials presented, but the authenticated user does not have permission to access the resource. The key difference is authorization, not authentication: you know who the user is, but the user isn’t allowed to perform this action. This can occur due to missing permissions, insufficient roles, or explicit deny rules set on the resource.
Understanding the nuance is essential for API design and UX. Misusing 401 to hide authorization failures or returning 401 for tokens that have insufficient scopes confuses clients and can leak hints about internal checks. The 403 response, when accompanied by a clear, minimal message and consistent headers, provides a stable signal to clients that authentication succeeded but authorization failed.
Authentication and Authorization: The Core Distinction
Authentication verifies who the user is, while authorization determines what the user is allowed to do. A system might accept a valid token (authenticating the user) but still deny access to a sensitive endpoint based on the user's roles or permissions. This separation is why 401 and 403 exist as distinct signals: one flags missing/invalid credentials, the other flags insufficient permissions. Designing an API with this distinction reduces ambiguity and helps clients respond appropriately, such as prompting for re-authentication versus guiding the user to request the necessary role or permission.
From a security perspective, keeping authentication and authorization logic separate minimizes information leakage. If a server returns the same generic error for both scenarios, clients cannot differentiate whether to re-authenticate or adjust permissions. Clear separation also aids auditing and access-control reviews, since each status code maps to a concrete permission state.
Client Experience and What Users See
Users interacting with web apps or APIs typically see either a login prompt or a denial message depending on the code. A 401 often triggers a redirect to a sign-in page or prompts the user to provide credentials again. In contrast, a 403 usually results in a plain access-denied message, sometimes with guidance on how to obtain permission (e.g., contact an administrator). From a UX standpoint, this difference matters: prompting for re-authentication when the user is already signed in wastes the user's time and can create frustration. Clear messaging that the user needs a specific permission or role is more helpful and reduces support requests.
Developers should avoid exposing sensitive internal logic in error messages. A good 403 message should be concise and non-revealing, while 401 messages can provide guidance on how to authenticate but should avoid disclosing token mechanics or backend details.
Server-Side decision making: How Responses Are Determined
On the server, the decision to return 401 or 403 starts with verification of authentication credentials. If the request lacks valid credentials or the token cannot be validated, the server returns 401. When authentication succeeds but the user is missing required permissions, the server returns 403. Middleware, access control lists (ACLs), and role-based access control (RBAC) rules are guiding factors. Implementations vary across frameworks, but the underlying principle remains consistent: separate the states of authentication and authorization to produce precise, actionable signals for clients.
Mistakes frequently occur when developers confuse the two states, for example returning 403 for unauthenticated requests or omitting the WWW-Authenticate header on 401 responses. Such misconfigurations reduce developer confidence and complicate client-side handling. Consistent behavior across endpoints builds predictable security posture and improves API usability.
Real-World Scenarios: APIs, Web Apps, and Microservices
In RESTful APIs, a missing or invalid token should yield a 401 with a WWW-Authenticate header indicating the supported scheme (Bearer, Basic, etc.). If a token is valid but lacks the required scope, a 403 with a short, non-ambiguous explanation is appropriate. Web applications leverage 401 to prompt sign-in flows, while 403 is often used for role-based access controls like admin-only pages. Microservices architectures rely on precise status signaling to orchestrate inter-service calls; a 401 prompts re-authentication of a service account, while a 403 prevents access despite authentication.
Designers should document these behaviors in API specs and ensure that error payloads align with the status codes. Consistency across API versions and services reduces integration time and improves developer satisfaction.
Common Mistakes and How to Avoid Them
One common pitfall is using 401 for every authentication issue, even after a user has logged in but lacks permissions. Another mistake is returning 403 for unauthenticated requests, which should be a 401. When error payloads become too verbose or reveal internal checks, it increases attack surface and confuses clients. Finally, failing to include informative headers like WWW-Authenticate for 401 responses degrades client guidance. To avoid these issues, define a clear error model, enforce RBAC consistently, and validate responses against your API contract.
Security and Design Considerations
Using 401 and 403 correctly enhances security by signaling precise states without leaking sensitive backend details. A 401 response should be treated as a call to re-authenticate, while a 403 signals that the user should modify their permissions or request access. In defense-in-depth strategies, these codes complement other controls (token lifetimes, token scopes, ACLs). When designing public APIs, consider global error handling strategies, standardized error shapes, and minimal but actionable messages that guide legitimate clients without disclosing internal structures.
Diagnosis, Debugging, and Best Practices
For debugging, begin by inspecting the authentication flow: verify tokens, expiration, and issuer. If credentials appear valid but access is denied, review the authorization rules, roles, and scopes for the requesting user. Ensure the server returns appropriate headers (e.g., WWW-Authenticate on 401) and that the error payload conveys the necessary guidance without exposing secrets. Implement unit tests that simulate missing credentials, invalid tokens, and permission failures to validate correct status codes. Document these tests for maintainability.
Practical Guidelines and Takeaways for Developers
- Use 401 for missing or invalid authentication; include a WWW-Authenticate header when appropriate.
- Use 403 for authenticated users who lack permissions to access a resource.
- Keep error messages concise and non-revealing; provide guidance on next steps.
- Align API contracts and client libraries with consistent status signaling across services.
- Regularly review access-control rules and token scopes to prevent authorization drift.
Comparison
| Feature | 401 Unauthorized | 403 Forbidden |
|---|---|---|
| Definition | Authentication is missing/invalid | Authenticated but not authorized |
| Typical Causes | No credentials or invalid credentials | Insufficient permissions or explicit denial |
| Authentication/Authorization State | Requires authentication | Authorization failure despite valid auth |
| Client Experience | Login prompt or challenge | Access denied after login |
| Security Implications | Signals need to authenticate | Signals permission outcome |
| Common Use Cases | Token missing/expired API requests | Token valid but lacks required scope/role |
| Example API Behavior | Return 401 with WWW-Authenticate header | Return 403 with clear deny message |
| Recommended Handling | Prompt re-authentication and token refresh | Review permissions and access-control rules |
Advantages
- Clarifies whether the issue is authentication or authorization
- Guides proper client UX with appropriate prompts
- Improves security signaling without leaking internal logic
- Reduces misinterpretation of access failures
Negatives
- Misconfiguration risks if used inconsistently
- Over-limiting access can hinder legitimate users
- Clients may ignore 401/403 if errors are vague
Use 401 for authentication failures and 403 for authorization failures
This distinction clarifies error signaling, supports secure API design, and improves developer experience. Always map each status to the actual failure type and document expectations for clients.
Frequently Asked Questions
What is the fundamental difference between 401 and 403 status codes?
The 401 status signals missing or invalid authentication, prompting re-authentication. The 403 status signals that authentication succeeded but the user lacks the required permissions. Together they separate authentication from authorization in API design.
401 means you must sign in or provide valid credentials; 403 means you’re signed in but not allowed to access the resource.
Should a 401 response trigger a login prompt in a web app?
Yes, a 401 is commonly used to trigger a login flow because authentication is required. The prompt should guide the user to re-authenticate without revealing backend specifics.
Yes—401 typically prompts users to log in again.
Can a correctly authenticated user receive a 401?
It can happen if the authentication token is missing or invalid, even after a login attempt. If the token is valid but permissions are missing, a 403 is more appropriate.
Yes, if the token is invalid or missing. If permissions are missing, use 403.
When should I use WWW-Authenticate header?
Use the WWW-Authenticate header with a 401 response to indicate the supported authentication schemes (e.g., Bearer). It helps clients know how to authenticate properly.
Add WWW-Authenticate on 401 responses to guide clients.
Are 401/403 errors useful for API clients?
Yes. They provide precise signals about failure modes, allowing clients to respond with re-authentication or permission requests. Clear messaging reduces confusion and support tickets.
They’re helpful signals; use them consistently.
How should error messages be phrased?
Keep messages concise and focused on next steps (e.g., sign in, contact admin). Avoid exposing internal checks or backend details that could aid attackers.
Be concise and action-focused; avoid exposing internals.
Top Takeaways
- Define failure types clearly in API contracts
- Return 401 for missing/invalid credentials
- Return 403 for authenticated but unauthorized access
- Keep messages concise and non-revealing
- Use authentication/authorization headers to guide clients