Error Code 400 vs 401: A Practical Comparison
A detailed, analytical comparison of HTTP 400 Bad Request and 401 Unauthorized, with guidance for developers and IT pros on when to use each status, how clients respond, and best practices for robust APIs in 2026.

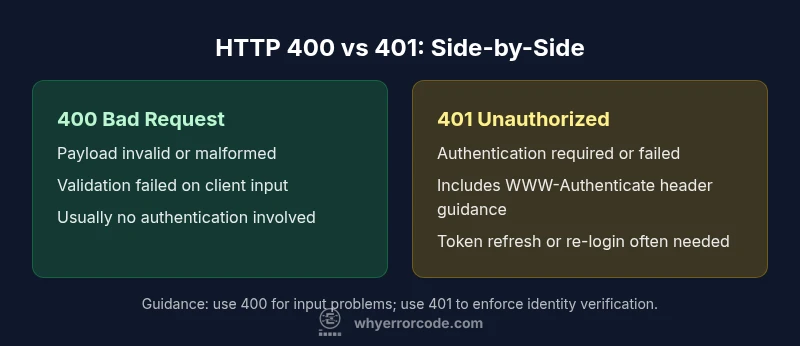
In HTTP, 400 Bad Request and 401 Unauthorized convey distinct client errors. A 400 indicates the request is malformed or invalid, such as bad syntax or invalid parameters. A 401 signals missing or invalid authentication credentials, meaning the client should authenticate. Choosing the correct status reduces debugging time and improves API reliability. This quick distinction helps teams implement clearer error handling, concise client guidance, and consistent server responses across services.
What are HTTP 400 and 401? Definitions
HTTP status codes are part of the server's response to a client request and guide developers on what happened. The 400 Bad Request code indicates the server cannot process the request due to a client-side error, such as malformed JSON, invalid parameters, or missing required fields. In contrast, the 401 Unauthorized status means the request requires user authentication, and the provided credentials are missing, invalid, or expired. The server understood the request but refuses to authorize it until proper authentication is supplied. While 400 points to input quality, 401 points to authentication quality. Recognizing this distinction helps teams separate concerns: payload validation versus identity verification. In practice, many APIs reserve 401 for auth failures and 400 for payload problems, though some edge cases exist where documentation defines nuanced behavior. The key is consistency across endpoints and predictable client behavior, which reduces mystery for developers and automated tooling.
When organizing an API, it is common to reserve 400 for validation errors, 401 for auth/permission problems, and 403 for valid credentials but insufficient rights. This separation improves debuggability, supports clearer UI messages, and aligns with established standards and security best practices. Always document the expected error semantics in your API docs to avoid ambiguity for integrators.
wordCount3rcv1": 0
Comparison
| Feature | HTTP 400 Bad Request | HTTP 401 Unauthorized |
|---|---|---|
| Definition | Malformed or invalid request payload, syntax errors, or invalid parameters | Request requires authentication or credentials are missing/invalid |
| Primary cause | Client input issues (bad JSON, missing fields, wrong types, invalid query params) | Authentication failures (no credentials, expired/invalid tokens, bad signatures) |
| Typical client action | Review payload, correct syntax, resend request with valid data | Provide valid credentials or refresh authentication token |
| Header/body signals | Often no authentication headers required; body may include details | WWW-Authenticate header is commonly included to indicate auth method |
| Security implications | Less information exposed about authentication state; focuses on payload quality | Directly informs client about auth state; potential risk if verbose in logs |
| Typical use cases | Validation errors on inputs, content-type, or formatting issues | Endpoints secured behind authentication (APIs, protected resources) |
Advantages
- Clarifies whether the issue is input quality or authentication
- Improves debugging with more precise client feedback
- Supports consistent API error semantics across endpoints
- Facilitates better logging and monitoring for client errors
- Reduces surface area for leaking authentication details in responses
Negatives
- Over-reliance on 400 for all validation failures can obscure auth problems
- Misuse or inconsistent documentation leads to misinterpretation
- Some servers may mirror overbroad messages in 400s, increasing risk
- Edge cases may blur lines between 400 and 401 in complex auth flows
401 is the precise choice for missing/invalid credentials; 400 is best for malformed requests.
Use 401 when authentication is the barrier, and 400 when the client message itself is invalid. Clear separation improves debugging, client guidance, and security hygiene.
Frequently Asked Questions
What is the fundamental difference between HTTP 400 and 401?
The 400 Bad Request signals a problem with the client’s request, such as invalid syntax or missing data. The 401 Unauthorized indicates that authentication is required or credentials are invalid. They address different layers of the request: payload integrity versus identity verification.
400 means bad request due to input problems; 401 means you need to authenticate or re-authenticate.
When should I return 400 instead of 401?
Return 400 when the request cannot be parsed or is semantically invalid, such as bad JSON, incorrect field types, or missing required data. Authentication status is not the primary issue in these cases.
Use 400 for input validation failures, not authentication failures.
Can a request be both 400 and 401?
Yes, in layered systems a single call might fail validation (400) before authentication is checked, or fail authentication (401) before validation completes. The API should define a clear order of checks to avoid ambiguity.
In practice, many systems return one, then the other only if the first check passes.
Is a WWW-Authenticate header required with 401?
Including a WWW-Authenticate header is common and recommended for 401 responses to guide clients on how to provide credentials. Its presence helps standardize how clients retry authentication.
401 usually comes with a WWW-Authenticate header to show how to authenticate.
How should clients respond differently to 400 vs 401?
For 400, clients should fix the request payload and retry. For 401, they should obtain or refresh authentication credentials before retrying. Ensure retry logic respects security policies and does not reveal sensitive information.
Fix input for 400; authenticate properly for 401.
Can a 401 be returned for a valid token that lacks permissions?
Yes. A 401 can indicate that credentials are valid but do not grant access to the requested resource. In such cases, a 403 Forbidden might be used for clarity if proper authentication exists but authorization fails.
If credentials exist but access is blocked, consider 403 for clarity.
Top Takeaways
- Differentiate 400 vs 401 based on payload vs authentication
- Include WWW-Authenticate header with 401 responses where applicable
- Validate inputs thoroughly to minimize 400 errors
- Document error semantics clearly in API docs
- Log and monitor error patterns to detect auth-related issues