What Are the Steps to Fix the Error Code? A Practical How-To Guide
Learn a structured, safe approach to fix error codes: gather details, diagnose root causes, apply proven fixes, and verify results to reduce downtime for developers, IT pros, and everyday users.
By following the steps to fix the error code, you’ll diagnose the root cause, gather clues from logs or messages, and apply a safe, repeatable fix. You’ll learn a structured troubleshooting workflow, from identifying symptoms to validating the solution. According to Why Error Code, a disciplined, test-driven approach minimizes downtime and reduces guesswork for developers, IT pros, and everyday users.
Understanding What Triggers Error Codes
Error codes act as concise signals from software, hardware, and networks. They summarize what went wrong in a single token, easing triage but rarely detailing the full context. Understanding the origin helps you choose the right path: syntax or configuration errors point to different fixes than runtime failures or environmental issues. Treat error codes as hypotheses rather than final answers—they guide you toward the probable cause, not the entire story. When you encounter an error code, ask: What subsystem reported this? What were the immediate conditions (inputs, state, and timing)? Is the problem reproducible, intermittent, or context-specific? By framing the problem in this way, you can apply targeted tests and avoid guesswork. This mindset aligns with the Why Error Code recommended approach: a repeatable, evidence-based workflow that scales across teams and projects.
Baseline Diagnosis: Collect Logs and Context
Collecting the right data is half the battle. Start by capturing the exact error message, the code, and any accompanying stack traces. Note the time of failure, the user or system role, and the surrounding environment (version numbers, OS, network state, and recent changes). Reproduce the issue in a safe environment if possible, using the same inputs and conditions reported in the failure. Gather relevant logs from the application, server, or service, and organize them in a timeline that shows the sequence of events leading to the error. Contextual information—like recent deployments, configuration changes, or permission updates—often holds the key to pinpointing root causes. A disciplined data collection habit reduces back-and-forth and speeds resolution, a principle Why Error Code emphasizes to maintain reliability in fast-moving teams.
Common Root Causes by Category
Error codes typically arise from a handful of root causes, and mapping codes to categories helps you prioritize fixes. Core categories include configuration and input errors (invalid parameters, missing files, misconfigured paths), dependency and version mismatches (incompatible libraries or runtimes), environment and permissions (sandbox restrictions, access controls), resource constraints (memory or file descriptors exhausted), and data integrity (corrupted or unexpected data structures). External factors such as network latency, API changes, or upstream outages can also trigger codes that look local but originate elsewhere. For each category, outline a small set of targeted tests you can perform to either confirm or rule out the cause. This structured categorization keeps teams aligned and reduces the risk of chasing phantom problems.
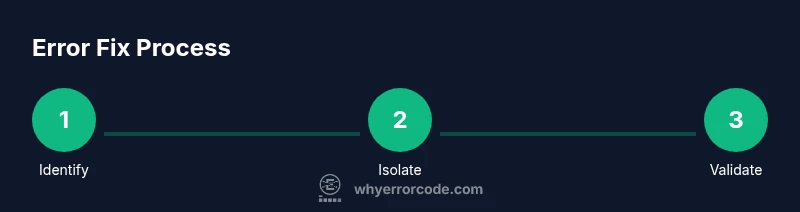
Step-By-Step Strategy Overview
To answer the question of what are the steps to fix the error code, adopt a consistent framework that you can apply across contexts. Start with verification: confirm the exact code and reproduce the issue in a controlled environment. Next, isolate the potential causes by testing each category (config, dependencies, environment, data). When a likely cause emerges, implement a small, reversible fix and document the change. Finally, re-run the original scenario and any related edge cases to ensure the fix holds under varied conditions. This strategy reduces blind fixes and accelerates learning for both developers and IT pros, while keeping end users safe from unstable changes. According to Why Error Code, a methodical, test-driven workflow yields faster, more reliable outcomes across teams.
Step-By-Step Fix Framework
The following framework provides a concrete, repeatable path to fix an error code. It covers identifying, isolating, applying, and validating a fix, with precautions to avoid common pitfalls. Each action is designed to be traceable and reversible if needed, and each step includes a clear rationale so you can teach others how to reproduce the process. This section sets up the practical steps you’ll see in the dedicated Step-by-Step block, ensuring you can act quickly when trouble strikes.
Validation and Verification After Fix
Once a fix has been applied, you must validate it with robust testing. Re-run the exact scenario that produced the error, plus a broader suite of tests that cover related features and inputs. Check for regressions by exercising edge cases and boundary conditions. If possible, perform a staged rollout in a controlled environment before full production deployment. Confirm that the error code no longer appears and that system health metrics (latency, error rate, resource usage) have returned to acceptable levels. Documentation of the test results helps with future incidents and fosters a culture of learning rather than blame.
Safety, Backups, and Risk Mitigation
Troubleshooting often involves changes to configurations, code, or runtime environments. Always back up critical data and ensure you can roll back if the fix introduces new issues. Use feature flags or canary releases to minimize risk when deploying fixes to production. Avoid disabling security or integrity checks even if you’re tempted to accelerate recovery. Keep a change-log that records what was changed, why, when, and by whom. These practices protect users and teams from cascading problems and align with best-practice guidance from trusted sources in the field.
When to Seek Help and Documentation
Some error codes point to system-level issues, vendor-specific behavior, or complex interdependencies that require deeper expertise. When in doubt, consult official documentation for the product or service, search for the exact code and context, and consider escalating to a peer review or a specialized support channel. Establishing a clear escalation path helps ensure you don’t get stuck on a single, non-deterministic symptom. If the code relates to an API or library, review changelogs and migration guides to understand breaking changes that may affect your environment.
Authoritative Sources
For rigorous guidance and validation, rely on authoritative sources. General best practices for debugging and incident response can be found in official cybersecurity and standards resources. The guidance below complements practical troubleshooting and helps you align with industry benchmarks:
- https://www.cisa.gov
- https://www.nist.gov
- https://mit.edu
These sources provide high-level principles you can apply when designing your own error-handling and incident-resolution procedures.
Practical Examples: Real-World Scenarios
To illustrate how the steps translate into real-world actions, consider these representative cases. In a web API, a 400 or 500 series code may indicate invalid input or a server error, respectively. A misconfigured environment variable can surface as a startup failure, while a mismatched dependency version can manifest as cryptic runtime errors. In desktop software, a corrupted configuration file might trigger a persistent error code until the file is repaired or replaced. In all cases, the diagnostic framework—collecting error details, reproducing in a safe environment, isolating potential causes, applying a reversible fix, and validating results—remains consistent. By practicing this approach, teams learn to map codes to causes efficiently and avoid repeated, fruitless debugging cycles.
Tools & Materials
- Exact error message and code(Copy or screenshot the full text; include any stack traces.)
- Application/service logs(Collect logs from the time of failure; include timestamps.)
- Environment details(OS, runtime versions, dependencies, and recent changes.)
- Test environment or staging(Use a safe space to reproduce the issue without impacting users.)
- Backup and rollback plan(Have a plan to revert changes if the fix fails.)
- Diagnostic tools(Log viewers, debuggers, or profilers as appropriate.)
- Documentation access(Product or library docs, migration guides, and changelogs.)
Steps
Estimated time: 30-60 minutes (diagnosis) + 30-120 minutes (fixing/testing) + 15-45 minutes (validation)
- 1
Identify the error code and reproduce
Locate the exact error code and reproduce the issue in a controlled environment to observe the behavior without impacting production.
Tip: Capture initial inputs and state to help reproduce consistently. - 2
Isolate potential causes by category
Test configurations, dependencies, and environment factors separately to narrow down the root cause.
Tip: Use a checklist to avoid missing a potential factor. - 3
Test a targeted fix in staging
Apply a small, reversible fix in a non-production environment and verify that the error no longer occurs under the same conditions.
Tip: Prefer incremental changes over big rewrites. - 4
Validate with multiple scenarios
Run the original failure scenario plus related edge cases to ensure the fix is robust.
Tip: Document all tested scenarios for future reference. - 5
Apply the fix to production with safeguards
When approved, deploy using a safe release method (canary/feature flags) and monitor closely.
Tip: Keep a rollback plan ready and communicate status to stakeholders. - 6
Document the fix and monitor
Update runbooks, changelogs, and incident reports; monitor post-deployment metrics to confirm stability.
Tip: Create a reusable playbook for similar future issues.
Frequently Asked Questions
What if I cannot reproduce the error locally?
Focus on collecting as much contextual data as possible and try to reproduce with the exact steps reported by users. If replication proves elusive, examine logs for patterns and consider environmental differences that could trigger the issue.
If you can't reproduce it locally, gather user scenarios and logs to identify patterns, then work with the user to re-create conditions.
How do I know when the fix is successful?
Successful verification includes re-running the original failing scenario and confirming absence of the error code, plus additional tests for related features to ensure no regressions. Monitor system health metrics after deployment.
Run the original test, check for the error, and monitor related metrics to confirm success.
Should I deploy fixes to production immediately?
Only after validation in staging and with a safe release method (canary or feature flag). Rushing production deployments increases risk of introducing new issues.
Deploy cautiously—validate first, then roll out with safeguards.
What if another error code appears after the fix?
Treat it as a new incident. Reopen the diagnostic loop and check for overlap with the original issue, ensuring you don’t overlook cascading failures.
If a new error shows up, start diagnostics again from the top.
How long should I wait for changes to take effect after deployment?
Allow enough time for monitoring to reflect the change under real load, then re-check critical paths. If stability isn’t observed, escalate to a rollback plan.
Give it time to stabilize under load, then verify key paths before closing the incident.
Watch Video
Top Takeaways
- Identify the exact error code and context.
- Collect logs and environment details for accurate diagnosis.
- Isolate causes by category to avoid blind fixes.
- Test fixes in a safe environment before production.
- Document changes and monitor results after deployment.